Windows under attack: 0-day vulnerability used by ransomware group
Microsoft released security updates for Windows yesterday and revealed today that the updates include a patch for a 0-day issue that is exploited in the wild.
The vulnerability -- Windows Common Log File System Driver Elevation of Privilege Vulnerability -- is tracked as CVE-2025-29824.
Important information:
- The issue affects most supported server and client versions of Windows, including Windows 10, Windows 11, and Windows Server 2025.
- Microsoft notes that the exploit does not work in Windows 11, version 24H2.
- It is a use-after-free security issue that may be exploited for local elevation attacks.
- The attack does not require user interaction.
- The attacker may gain system privileges upon successful exploitation.
Microsoft notes that it is aware of limited attacks. It mentions targets in the IT and real estate sectors in the United States, the financial sector in Venezuela, a Spanish software company, and the retail sector in Saudi Arabia specifically in a special announcement on its security website.
Installation of the update protects systems against exploits. Microsoft's guidance includes an ominous note revealing that the company is delaying the patch for Windows 10 systems. It does not provide an explanation for the delay. Affected users and administrators are asked to monitor the official CVE on Microsoft's MSRC website for updates regarding the rollout of the patch to Windows 10 systems.
Home users may use Windows Update to install the patch immediately on Windows 11. This is done via Settings > Windows Update. Note that a restart of the system is necessary to finalize the installation of the security update.
On the technical side, the vulnerability is found in the Common Log File System (CLFS) kernel driver according to Microsoft. The company says that has not determined the initial attack vector, but discovered "some notable pre-exploitation behaviors by Storm-2460".
Good to known: Storm 2460, which is better known as RansomEXX, is a notorious ransomware group.
Microsoft observed the following behavior in multiple cases:
- The threat actor uses the certutil tool to download a malicious file from a legitimate but compromised third-party website.
- The downloaded file was a malicious MSBuild file.
- The malware in question goes by the name PipeMagic, which has been known since 2023.
- After deployment of the malware, it is exploiting the vulnerability described in this guide for process injection into system processes.
One of the activities of the malware on the user system is the dumping and parsing of LSASS memory to obtain user credentials. Ransomware activity followed on the target systems, notably file encryption and the adding of random extensions.
Closing Words
Microsoft recommends to install the Windows security patches immediately to protect systems from exploit attempts. The delay on Windows 10 is unfortunate, as it means that systems remain vulnerable to attacks until Microsoft releases the patch for the system.
Now You: when do you install updates on your systems? Did you install the April 2025 security updates already?
RECOMMENDED NEWS

Microsoft's new "use Bing" prompt in Edge is missing a vital option
Microsoft Edge shows a new prompt to some users that asks them to make Microsoft Bing the default s...

Google now lets you set up 2-Step Verification without adding a phone number
Google has announced that it is streamlining the process of setting up 2-Step Verification (2SV) fo...
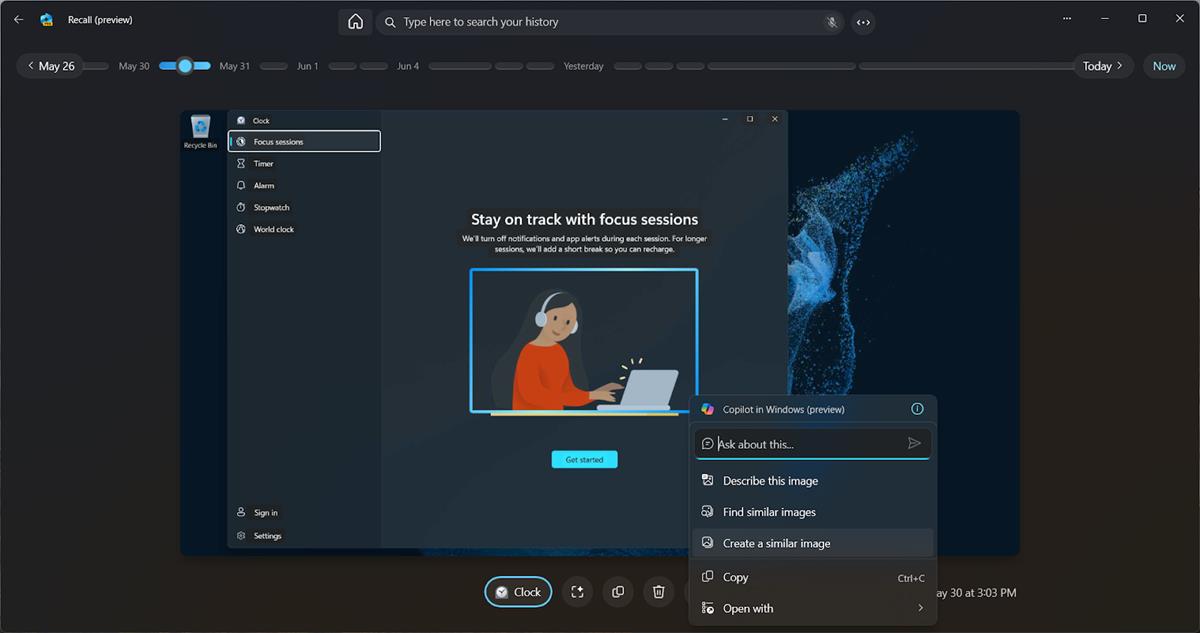
You can remove Recall from Windows if you do not want it (Update: or not)
Microsoft is currently preparing a second version of its controversial AI-feature Recall. The compa...

Microsoft confirms Auto HDR bug in Windows 11 and blocks updates as a consequence
Windows 11, version 24H2 has not been out for long, but its number of issues is already longer than...
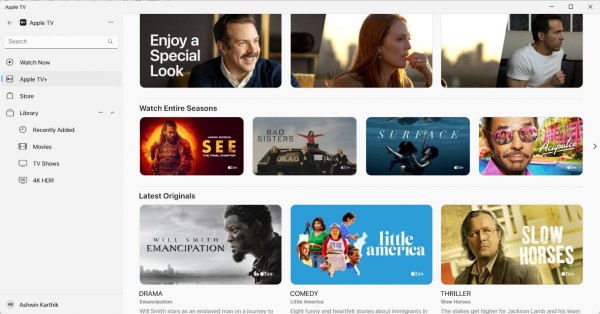
Apple TV+ Now Available on Android Devices with Exclusive Content and Free Trial
Apple has officially launched its Apple TV+ streaming app for Android devices, marking a major expa...
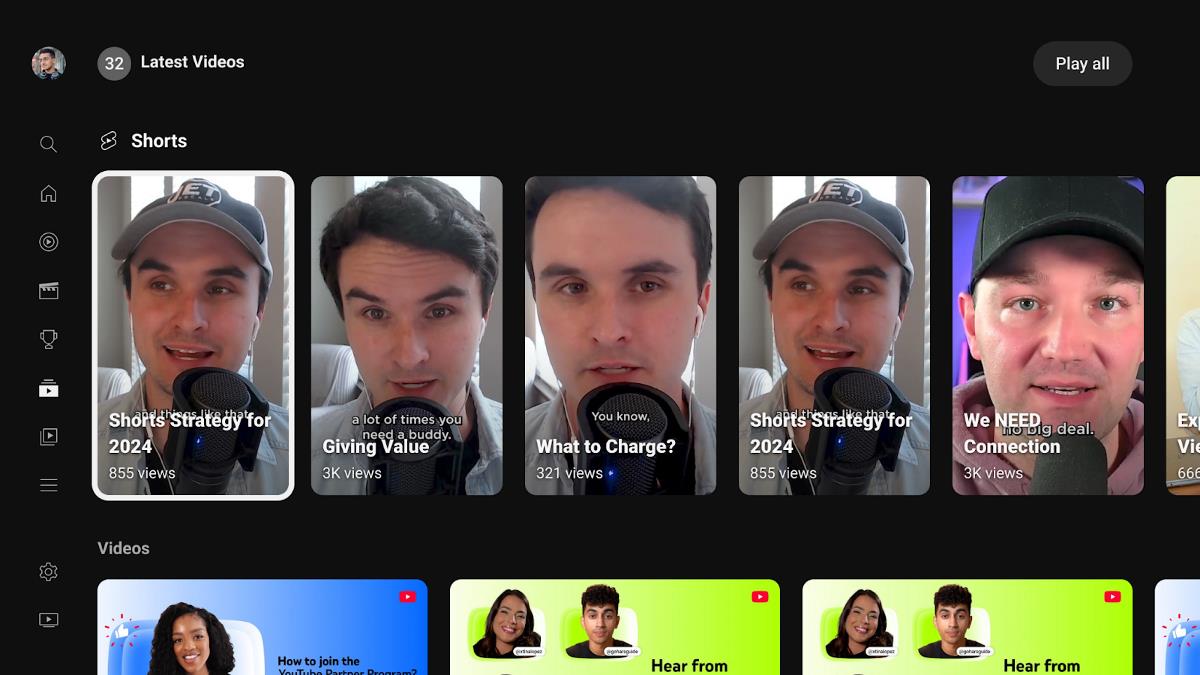
YouTube TV's new update prioritizes shorts, and users don't like it
YouTube is changing the way how its app for TVs and consoles display videos on your homepage. The s...
Comments on "Windows under attack: 0-day vulnerability used by ransomware group" :