Security experts have discovered new Intel Spectre vulnerabilities
Researchers from ETH Zurich have uncovered a new class of vulnerabilities linked to Intel processors. They were able to bypass Intel's defenses against Spectre.
Spectre is a class of vulnerabilities that was originally identified in 2018, along with Meltdown, a similar exploit that affected AMD chips. These flaws exploited speculative execution, which in turn leaked data. Though the vulnerabilities were patched 7 years ago, Microsoft released a Registry security mitigation a year ago to protect against the vulnerability.
As it turns out, Spectre has resurfaced in a new persona. The researchers from ETH Zurich have labeled the data-leaking flaws as Branch Prediction Race Conditions (BPRC). These vulnerabilities primarily affect Intel CPUs from the 9th generation (Coffee Lake Refresh) down to the 7th generation (Kaby Lake).
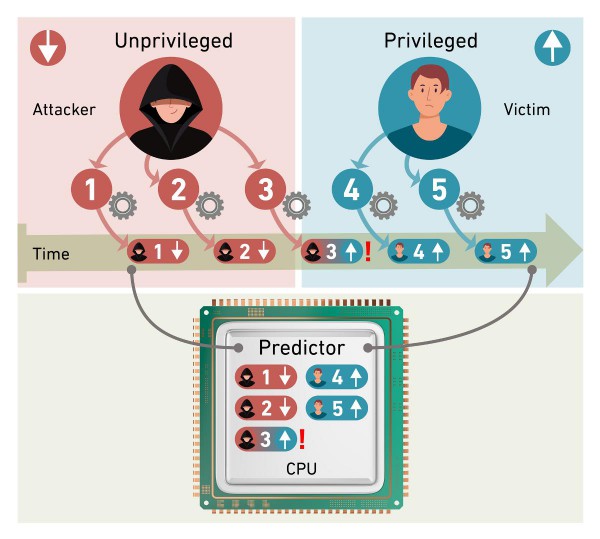
The researches said that the branch predictors on Intel processors are updated asynchronously inside the processor pipeline, as a result of which there are potential race conditions. In such a scenario, two or more processes or threads could attempt to access and update the same information concurrently, and this could lead to chaos. They discovered an exploit was possible where a processor switches privilege levels, such as from user to kernel, while branch predictor updates are still in flight. This can lead to a new attack vector, Spectre v2, which allows unauthorized code injection thanks to elevated privileges. The security experts call it Branch Privilege Injection (BPI). These issues affect all sorts of computers, from PCs to servers in data centres.
Here is how the issue was described: “We can use the vulnerability to read the entire contents of the processor’s buffer memory (cache) and the working memory (RAM) of another user of the same CPU.”
The discovery by the Swiss team indicates that there is a performance impact, up to 2.7 percent overhead for the microcode mitigation on Alder Lake, though Intel is yet to comment on this issue.
Intel has released a microcode update to address the new flaw, which has been designated as CVE-2024-45332. The Indirect Branch Predictor Advisory describes the issue as follows: Potential security vulnerabilities in some Intel® Processor indirect branch predictors may allow information disclosure. Intel is releasing microcode updates to mitigate these potential vulnerabilities.
It is worth noting that products from AMD and ARM don't appear to be affected by this new exploit.
Source: The Register, ETH Zurich
RECOMMENDED NEWS

How to enable Tab Previews in Firefox
Mozilla released Firefox 123 a few days ago, and it comes with a new feature. The browser now suppo...
Apple releases macOS Sonoma 14.4 update with over 50 security fixes
Apple has released the macOS Sonoma 14.4 update. The software update includes a couple of new featu...

DOJ pushes for Google to sell Chrome to break search monopoly
The U.S. Department of Justice (DOJ) is intensifying its efforts to compel Google to divest its bro...
Google announces extended repair program for Pixel 7a
Google has confirmed that certain models of the Pixel 7a are affected by a battery issue. A support...

Oblivion Remastered update breaks DLSS and Frame Gen on PC
The recent update for The Elder Scrolls 4: Oblivion Remastered has raised concerns among players us...
Microsoft Windows Security Updates for May 2025 are now available
Microsoft released security updates and non-security updates for all supported versions of its Wind...
Comments on "Security experts have discovered new Intel Spectre vulnerabilities" :